Gaming
/zwzhanbf-ym: Unlocking the Mystery and technique to Decode it?

/zwzhanbf-ym; Have you ever come across a string of seemingly-random characters like /zwzhanbf-ym and wondered what it means? Is it a secret code or just nonsense? Well, get ready to unravel the mystery! In this post, we will take a deep dive into the world of code decoding and figure out exactly what /zwzhanbf-ym is all about. So, buckle up and let’s unlock the secrets together!
Introduction: What is /zwzhanbf-ym Code?
Have you ever come across a string of seemingly random letters and numbers while browsing the internet, and had no idea what it meant? If so, you were probably looking at a /zwzhanbf-ym code. These codes are used to track data about web traffic and activity, and can be found on everything from websites to apps to social media platforms. But what do they actually mean, and how can you decode them?
In short, /zwzhanbf-ym codes are used to collect information about how users interact with websites and digital properties. This data is then used by businesses and organizations to improve their online offerings. The specific information that is collected can vary, but may include things like the type of device being used, the date and time of the interaction, the geographical location of the user, and which pages or features on the site are being accessed.
Collecting this data is fairly straightforward: businesses simply add a snippet of code to their webpages that tracks user interactions. This code is typically generated by a third-party service like Google Analytics or Adobe Analytics. Once added to a page, the code begins tracking data immediately; there is no need for users to take any action for it to work.
The resulting data set can be quite large and unwieldy, however. That’s where /zwzhanbf-ym codes come in. These codes are used to anonymize the data so that individual users cannot be identified
What Encryption Method is Used for /zwzhanbf-ym Code?
When it comes to encryption, the /zwzhanbf-ym code uses a very simple substitution cipher. This means that each letter in the original message is replaced with a different letter, number, or symbol. The order of the letters remains the same, making it relatively easy to decode.
To decode the /zwzhanbf-ym code, simply look at the substitution cipher key and substitute the correct letter for each one used in the code. For example, if the key says that A is replaced with D, then every time you see an A in the code, you would replace it with a D. Using this method, you should be able to quickly decode any /zwzhanbf-ym code.
How to Decode the /zwzhanbf-ym Code
The /zwzhanbf-ym code is a substitution cipher that is used to encode messages. In this cipher, each letter in the message is replaced with a different letter or symbol. The most common way to decode this type of cipher is to use a frequency analysis. This involves looking at how often each letter appears in the coded message and comparing it to how often that letter appears in other texts. By looking at the patterns that emerge, you can start to piece together the meaning of the message.
– Brute Force Attack
A brute force attack is a type of password guessing attack in which the attacker tries to guess the password for a given account by trying out different combinations of characters. This type of attack is usually carried out by automated software that can generate large numbers of password guesses quickly.
Brute force attacks are not always successful, but they can be if the attacker has access to a large number of potential passwords (for example, if they have obtained a list of common passwords) or if they are using a sophisticated algorithm that can generate new passwords very quickly.
If you think you may be a victim of a brute force attack, there are some steps you can take to protect yourself:
– Use a strong password that is not easily guessed. A good password should be at least 8 characters long and include a mix of uppercase and lowercase letters, numbers, and symbols.
– Use two-factor authentication whenever possible. This adds an extra layer of security to your account by requiring you to enter both your password and a code that is sent to your phone or email when someone tries to log in.
– Be careful about what information you share online. Attackers may try to gather information about you from social media or other public sources in order to better guess your password.
– Frequency Analysis
The /zwzhanbf-ym code is a mystery to many people. It is a code that appears to be randomly generated, but it actually has a hidden meaning. If you know how to decode it, you can unlock the mystery and discover what it means.
To decode the /zwzhanbf-ym code, you need to understand how frequency analysis works. Frequency analysis is a technique that can be used to decipher codes and ciphers. It relies on the fact that certain letters and groups of letters occur more often than others in a language. For example, the letter “e” is the most common letter in English, while “q” is one of the least common letters. By analyzing the frequencies of letters in a piece of text, it is possible to figure out what the text says.
To use frequency analysis to decode the /zwzhanbf-ym code, you first need to find a piece of text that contains the code. Once you have found such a text, you can count the number of times each letter occurs in the text. The letters that occur most frequently are likely to be vowels, while the letters that occur least frequently are likely to be consonants. Based on this information, you can start to decipher the code.
It should be noted that frequency analysis is not always successful in decoding codes and ciphers. However, it is often worth trying because it can provide valuable insights into
– Differential Cryptanalysis
Differential cryptanalysis is a technique for attacking cryptographic algorithms by finding differences in the way that they process data. This can be used to …
– Linear Cryptanalysis
Linear cryptanalysis is a type of cryptanalysis. It uses mathematical analysis to find weaknesses in cryptographic algorithms based on the linear structure of the underlying math. This type of attack can be used to find ways to decrypt data or weaken the security of an encryption system. Linear decryption is one of the most well-known and widely used attacks against cryptographic systems.
Cryptographers have been familiar with linear decryption since at least the 1970s, but it wasn’t until the early 1990s that researchers began using the technique effectively. In 1994, Mitsuru Matsui and Yoshiaki Tsuno published a paper describing a new method of linear cryptanalysis called “differential cryptanalysis.” Since then, it has become one of the most popular techniques for attacking cryptographic systems.
Translated with www.DeepL.com/Translator (free version)
Differential cryptanalysis works by selecting a set of input values (called pairs) that, when processed by a cryptographic algorithm, are likely to produce a significant difference in output. The attacker then examines the differences in the outputs to see if conclusions can be drawn about the internal state of the password. This information can be used to decrypt data or to find other ways to attack the system.
Linear cryptanalysis is a powerful tool for breaking cryptographic systems, but it is not always easy to use. Differential cryptanalysis, in particular, can be difficult to apply effectively against real-world ciphers. Nonetheless, this type of attack has been used successfully
Common Uses of the /zwzhanbf-ym Code
The /zwzhanbf-ym code is a mystery to many people. It’s an obscure code used by the Chinese government that few people know how to decode. However, there are some common uses for the /zwzhanbf-ym code.
One common use is for censorship. The Chinese government often uses the /zwzhanbf-ym code to censor websites and online content that it doesn’t want its citizens to see.
Another common use is for data compression. The /zwzhanbf-ym code is often used to compress data so that it takes up less space on a storage device or network.
The /zwzhanbf-ym code can also be used for encryption. This means that information encoded with the /zwzhanbf-ym code can only be decoded by someone with the proper key.
Conclusion
Trying to decode a complex code like /zwzhangb-ym can be a daunting task, especially if you are unfamiliar with cryptography. With the information and guidance outlined in this article, we hope that cracking these codes has become easier for you! If however, you still find it difficult to solve such codes, there’s no need to worry as help is available online through specialized services where experts will crack any code for you quickly and easily. So keep exploring new ways of deciphering mysterious codes while having fun at the same time!

Gaming
Apkgstore: Your Gateway to a World of Apps

In today’s fast-paced digital landscape, mobile applications have become an integral part of our daily lives. From productivity tools to entertainment apps, the demand for diverse and innovative applications is ever-growing. Enter apkgstore, a platform that not only meets these demands but also stands out in the competitive world of app marketplaces.
What is apkgstore?
In essence, apkgstore is a curated hub for Android applications. The term “apkg” refers to the file format used for Android apps, and this store provides a centralized space for users to discover, download, and enjoy a plethora of applications.
Why Choose apkgstore for Apps?
User-friendly Interface
Navigating through apkgstore is a breeze. The clean and intuitive interface ensures that even first-time users can find their way around with ease. No confusing menus or hidden options – just a straightforward experience.
Diverse App Categories
Whether you’re a gaming enthusiast, a productivity guru, or someone looking for niche apps, apkgstore has you covered. The platform boasts a wide array of categories, ensuring that there’s something for everyone.
Unique Features and Benefits
apkgstore doesn’t stop at just offering . Exclusive features like personalized recommendations, app bundles, and early access to beta versions provide users with added value, making their app discovery journey more enjoyable.
Navigating Through apkgstore
Curious about how to make the most of apkgstore? Let’s take a quick tour.
- Creating an Account
- Sign up for a personalized experience.
- Access your app history and preferences effortlessly.
- Exploring Categories
- Browse through categories like Games, Productivity, Lifestyle, and more.
- Discover new apps based on your interests.
- Search Functionality
- Use the powerful search bar to find specific apps.
- Filter results based on ratings, popularity, or release date.
- App Details
- Click on an app to view detailed descriptions, user reviews, and screenshots.
- Make informed decisions before downloading.
The Variety of Apps on apkgstore
From gaming to fitness, apkgstore hosts a vast collection of apps. Whether you’re into the latest gaming trends or exploring apps to enhance your daily routine, apkgstore has you covered.
Popular Categories and Apps Available
- Gaming Galore
- Explore trending games and classics.
- Stay updated on the latest releases.
- Productivity Powerhouse
- Find apps to boost your efficiency.
- Task managers, note-taking apps, and more.
- Lifestyle and Entertainment
- Discover apps for hobbies and leisure.
- From photography to streaming, explore it all.
The Rise of apkgstore in the App Market
With millions of users worldwide, apkgstore has become a powerhouse in the app market. Let’s take a look at some compelling reasons behind its rise.
Market Trends and Statistics
Recent market trends indicate a significant increase in apkgstore’s user base. The platform’s user-friendly approach and diverse app offerings have contributed to this surge in popularity.
User Testimonials and Reviews
Don’t just take our word for it. Hear what users have to say about their apkgstore experience. Positive reviews highlight the platform’s reliability, vast selection, and ease of use.
Security and Privacy on apkgstore
The safety of user data is a top priority for apkgstore. Robust security measures are in place to ensure that your personal information remains confidential.
Measures Taken to Ensure User Data Safety
- Encryption Protocols
- All data transmission is encrypted for enhanced security.
- Protecting user information from potential threats.
- Regular Security Audits
- Ongoing assessments to identify and address vulnerabilities.
- Keeping the platform resilient against evolving threats.
Comparisons with Other App Platforms
How does apkgstore fare in terms of security and privacy when compared to its competitors? Let’s delve into a comparative analysis.
How Developers Benefit from apkgstore
Developers are a crucial part of the apkgstore ecosystem. The platform offers a range of benefits and incentives to make it an attractive space for app development.
Developer-friendly Policies
- Fair Revenue Sharing
- Developers receive a fair share of app revenues.
- Encouraging a thriving developer community.
- Transparent Guidelines
- Clear and concise policies for app submission.
- Streamlining the development and submission process.
Revenue-sharing Models and Incentives
apkgstore understands the importance of rewarding developers for their efforts. Competitive revenue-sharing models and additional incentives drive innovation within the app development community.
Exclusive Features of apkgstore
What makes apkgstore stand out among the myriad of app stores? Let’s explore some exclusive features that set it apart.
Highlighting Unique Functionalities
- Personalized Recommendations
- Receive app suggestions based on your preferences.
- Enhancing the app discovery experience.
- App Bundles and Discounts
- Save money with bundled app packages.
- Periodic discounts for premium apps.
Special Promotions and Offers
Keep an eye out for exclusive promotions and limited-time offers on apkgstore. From discounted in-app purchases to free premium apps, there’s always something exciting in store for users.
apkgstore vs. Competitors
How does apkgstore compare to other app platforms? Let’s break down the key differentiators.
Comparative Analysis with Other App Stores
- User Interface
- Intuitive design vs. cluttered interfaces.
- apkgstore prioritizes simplicity.
- App Selection
- Diverse categories and a vast app library.
- Catering to a wide range of user interests.
What Sets apkgstore Apart
The emphasis on user experience, developer support, and unique features positions apkgstore as a leading player in the app marketplace.
Tips for Getting the Most Out of apkgstore
Ready to dive into the world of apkgstore? Here are some tips to enhance your experience.
Utilizing Advanced Search Options
- Filters and Sorting
- Refine your search using filters.
- Sort results based on relevance or popularity.
- Wishlists and Notifications
- Create wishlists for future app downloads.
- Receive notifications for app updates and promotions.
Taking Advantage of Promotions and Discounts
Stay tuned to apkgstore’s announcements for special promotions and discounts. Whether it’s a holiday sale or a developer spotlight, there are always opportunities to save on premium apps.
Future Developments and Updates
In the dynamic world of technology, apkgstore is committed to continuous improvement. Let’s look at what the future holds.
Anticipated Improvements and Features
- Enhanced User Profiles
- More customization options for user profiles.
- Tailoring the app experience to individual preferences.
- Streamlined App Updates
- Faster and more efficient app update processes.
- Ensuring users have access to the latest features promptly.
Staying Updated with apkgstore’s Advancements
Follow apkgstore on social media and subscribe to newsletters for the latest updates. Being informed ensures that you don’t miss out on exciting new features and improvements.
User Community and Engagement
Beyond being a repository of apps, apkgstore fosters a sense of community among its users.
Forums, Discussions, and User Interactions
- Engage in Discussions
- Participate in forums to discuss app recommendations and tips.
- Connect with like-minded users.
- Feedback and Suggestions
- Provide feedback on apps and the platform.
- Contribute to the continuous improvement of apkgstore.
How apkgstore Fosters a Sense of Community
Through interactive forums, engaging discussions, and user-driven content, apkgstore aims to create a community where app enthusiasts can connect and share their experiences.
Challenges and Criticisms of apkgstore
No platform is without its challenges. Let’s address some common concerns and discuss apkgstore’s plans for overcoming them.
Addressing Common Concerns
- App Quality Control
- Stricter guidelines to ensure app quality.
- Collaborating with developers for improvements.
- Timely App Updates
- Streamlining the app update approval process.
- Ensuring users have access to the latest features promptly.
Conclusion
In the vast universe of app stores, apkgstore stands out as a beacon of user-friendly design, diverse app options, and a commitment to user and developer satisfaction. Whether you’re a casual app user or a seasoned developer, apkgstore has something to offer. Explore the platform, discover new apps, and be part of a vibrant community.
Frequently Asked Questions (FAQs)
- Is apkgstore available for iOS users?
- Currently, apkgstore is focused on Android apps. However, plans for expansion to other platforms may be considered in the future.
- How often does apkgstore update its app library?
- The app library is regularly updated with new releases and updates. Users can expect fresh content and features on a regular basis.
- Are all apps on apkgstore free to download?
- While many apps on apkgstore are free, some may come with a price. The platform often features discounts and promotions to make premium apps more accessible.
- Can I trust the user reviews on apkgstore?
- User reviews on apkgstore are submitted by real users. The platform encourages honest feedback to help others make informed decisions.
- How can developers submit their apps to apkgstore?
- Developers can submit their apps through a straightforward process outlined in the developer guidelines on the apkgstore website.
Gaming
Embracing the Future with wager81

Imagine a world in which playing video games is more than just a hobby—it’s an exciting voyage into the unknown where every decision you make might be the difference between winning and losing. Enter the realm of wager81 a name that resonates with mystery and excitement. In this article, we’ll unravel the secrets behind “wager81,” exploring its origins, mechanics, impact on the gaming world, and the strategies to dominate the SEO landscape.
Decoding the Enigma
Origin and Evolution
Let’s begin at the roots. The story of wager81 is a tapestry woven with threads of innovation and passion. Understanding its evolution is key to grasping the significance it holds in the gaming community.
The Essence of “wager81”
What sets wager81 apart from the multitude of gaming platforms? We’ll examine its distinctive qualities and features in detail, presenting a clear picture of what sets it apart in the competitive gaming market.
Behind the Scenes
Mechanics and Algorithms
For the curious minds, we’ll lift the curtain on the intricate mechanics that power “wager81.” From algorithms that enhance user experience to the seamless integration of cutting-edge technology, we’ll explore the engine that propels this gaming marvel.
User Experience Explained
Embark on a virtual journey through the eyes of a “wager81” user. What can one expect? How does the platform cater to both seasoned game and novices? Get ready for an immersive exploration of the user interface and experience.
Revolutionizing the Industry
User Testimonials
What are gamers saying about “wager81”? We’ll compile firsthand accounts, revealing the transformative impact it has had on the gaming community. From casual players to esports enthusiasts, discover the stories that paint a vibrant picture of “wager81” in action.
Competitors and Comparisons
In a sea of gaming platforms, how does “wager81” stand out? We’ll conduct a comparative analysis, pitting it against competitors and highlighting the distinct advantages that make it a game-changer.
SEO Strategies for wager81
Dominating Search Results
In the digital landscape, visibility is key. We’ll unravel the SEO strategies that propel “wager81” to the top of search results, exploring the art of keyword magic and the science behind backlink building.
Keyword Magic
Unlock the secrets of selecting keywords that resonate with the gaming community. From trending phrases to niche-specific terms, we’ll guide you through the alchemy of keyword selection for optimal SEO performance.
Backlink Building
Building a robust online presence involves more than keywords. We’ll explore the art of backlink building, providing actionable insights into establishing “wager81” as an authoritative voice in the gaming industry.
Predictions and Speculations
Innovations on the Horizon
The future holds endless possibilities. What innovations can we expect from “wager81” in the coming years? Join us in a speculative journey, envisioning the next frontier of gaming excellence.
Market Trends and Analysis
Peek into the crystal ball of market trends. We’ll analyze industry data and predict the trajectory of “wager81,” offering insights that go beyond the conventional crystal ball gazing.
Pro Tips from Experts
Common Pitfalls to Avoid
There are obstacles to overcome while navigating the gaming world. Experts provide advice on how to get the most out of your wager81 experience as well as typical hazards to stay clear of for a smooth gaming experience.
Unlocking Hidden Features
Beyond the obvious lies a realm of hidden features. Discover the insider tips and tricks to unlock the full potential of “wager81,” elevating your gaming experience to new heights.
Ensuring User Safety
Encryption and Data Protection
In the age of digital vulnerabilities, security is paramount. Explore the measures “wager81” takes to safeguard user data, from encryption techniques to robust data protection protocols.
Addressing Security Concerns
We’ll address common security concerns, providing transparency on how “wager81” tackles challenges, ensuring users can immerse themselves in the gaming world with peace of mind.
Building a Thriving Community
Social Media Presence
A gaming platform is only as strong as its community. We’ll explore how “wager81” fosters a vibrant social media presence, connecting gamers from around the globe.
User Forums and Interactions
Beyond social media, discover the role of user forums in shaping the “wager81” community. These forums become the lifeblood of the gaming community, used for anything from problem-solving to experience-sharing.
Promoting Responsible Practices
Features for Responsible Gaming
Gaming should be a source of joy, not distress. We’ll explore the tools “wager81” uses to encourage responsible gaming, making sure players interact with the platform in a way that is both sustainable and healthful.
Collaborations and Partnerships
Responsible gaming extends beyond features. We’ll explore cooperation and alliances that amplify the message of responsible gaming, establishing “wager81” as a trailblazer in the industry.
Real-life Triumphs
Transformative Experiences
In the realm of “wager81,” triumphs aren’t confined to the virtual world. We’ll share real-life stories of individuals whose experiences on the platform transcended the boundaries of pixels and code.
Inspiring Tales
Get ready to be motivated by stories of tenacity, cunning, and friendship. Wager81 becomes more than a platform; it becomes a catalyst for personal growth and triumph.
Navigating Obstacles
Solutions in Progress
Even giants face challenges. We’ll discuss the obstacles “wager81” encountered and the ongoing solutions, highlighting the adaptability that defines its journey.
Learning from Setbacks
Failures serve as stepping stones to achievement. We’ll look at how wager81 uses obstacles as stepping stones to become stronger and more resilient in the always changing gaming industry.
References in Media
Memes and Internet Culture
Dive into the lighter side of “wager81” as we explore its references in memes and internet culture. From viral moments to inside jokes, discover the humor that binds the gaming community.
Impact on Language and Trends
Language evolves with culture. We’ll examine how “wager81” influences not just gaming vernacular but the broader linguistic trends, leaving an indelible mark on the digital lexicon.
Conclusion
In the grand tapestry of gaming, wager81 emerges as a vibrant thread, weaving together innovation, community, and excitement. The mystery behind wager81 emerges as we welcome the future and extends an invitation to players everywhere to join us on an incredible adventure.
Frequently Asked Questions (FAQs)
- Is “wager81” suitable for casual gamers or is it geared towards professionals?
- With a smooth experience for both experts looking for a competitive advantage and casual games looking for pleasure, Wager81 appeals to a wide range of users.
- How does “wager81” ensure the security of user data?
- “Wager81” employs advanced encryption and robust data protection protocols, ensuring the utmost security for user data in the digital realm.
- What sets “wager81” apart from other gaming platforms?
- Wager81 stands apart in the gaming business because to a blend of cutting-edge technologies, a vibrant community, and a dedication to safe gaming practices.
- Can you share a success story of someone who has benefitted from “wager81”?
- Certainly! The article features uplifting stories of individuals whose experiences on “wager81” transcended virtual triumphs, contributing to personal growth and success.
- How can users contribute to the “wager81” community beyond gaming?
- Users can actively engage in the “wager81” community through social media participation, contributing to user forums, and advocating for responsible gaming practices to foster a positive gaming environment.
Gaming
Exploring the World of CBC Games: Unleashing Your Inner Gamer

It’s time for you to unleash your inner gamer at CBC Games and dive into an exciting world filled with challenges, excitement, and endless fun. There are a variety of captivating online games at CBC Games that will keep you entertained for hours.
You’ll find something for everyone on CBC. From puzzles and strategy games to action-packed adventures and mind-bending mysteries, there’s something for everyone.
Let’s explore some of the most popular CBC Games that will ignite your gaming spirit. So gear up and get ready as we take a dive deep into an exciting world filled with thrills and entertainment.
Navigation bar
You can easily discover the wide variety of games available on CBC Games using the main navigation menu. Get ready for an immersive gaming experience with just a few clicks as you navigate through different categories and find the perfect game to suit your preferences.
Choose a season
Discover the exciting world of CBC Games. From Game Savers Trailer to The Thrillusionists, there is something for everyone.
Trailer for Game Savers
Game Savers Trailer is an exciting CBC game that challenges players to save the day as they navigate various levels and obstacles.
Mode of Practice
It provides a safe environment where you can experiment with different strategies, learn the controls, and get familiar with the game mechanics in Practice Mode.
Let’s get started
You’re invited to immerse yourself in a virtual world of excitement and challenges. Test your skills, strategize your moves, and compete against players from around the world. It’s time to unleash your inner gamer!
Shifters of shapes
“Shape Shifters” is a CBC game that challenges players to transform into different animals. In this thrilling game, you can transform into creatures such as wolves, eagles, and even dragons! Get ready to unleash your inner beast and conquer the virtual world.
Twisted up in all directions
It is a mind-bending puzzle game that challenges your spatial awareness and problem-solving skills. Navigate through twisted mazes, untangle knots, and unravel complex patterns to advance to the next level.
Height phobia
This adrenaline-pumping game in CBC Games will test your nerves and agility. Navigate through a treacherous obstacle course suspended high in the sky, avoiding obstacles and making daring jumps. Can you overcome your fear and finish the course?
Being a winner is cooler
Playing “It’s Cooler to be a Winner” with CBC Games will take you on a thrilling adventure. Get ready for some intense competition as you navigate through exciting levels to emerge as the ultimate champion! Show off your skills and claim victory!
Marketed
The CBC game “Gone to Market” takes players on an exciting shopping adventure as they navigate through the aisles, collect items, and avoid obstacles to complete your shopping list. Test your speed and agility in this fun and challenging game!
Ghosts
CBC’s “The Ghost” will challenge your stealth and problem-solving skills. Navigate through haunted halls, avoid spooky obstacles, and uncover the secrets of the ghostly presence.
Dinosaurs are hungry dinosaurs
A CBC Games favorite, Hungry Hungry Dinos is sure to keep you on the edge of your seat! Help these adorable dinosaurs satisfy their hunger by feeding them the right food.
A spider appeared
The CBC game “Along Came a Spider” will test your reflexes and problem-solving skills as you navigate through a web of challenges aimed at catching the spider. Can you overcome your arachnophobia and win?
It’s like walking on eggshells
In Walking on Eggshells, players must balance fragile eggs while navigating a treacherous path. This egg-citing challenge requires focus, precision, and quick reflexes to succeed. Can you make it across without cracking under pressure? Find out in this egg-citing game!
In the wrong hands
The Wrong Hands is an exciting CBC game that will challenge your problem-solving skills. Navigate through a maze and avoid the traps set by an evil mastermind.
Ducks with lucky ducks
Test your memory skills as you match the rubber ducks with their corresponding shapes in Lucky Ducks. See if you can keep up with the quacks!
Let’s play ball
Play Ball will bring out the athlete in you. Step up to the plate and swing for the fences as you aim to hit home runs and score points. Get ready for some intense competition on the virtual field!
Challenge Honey Hands
It’s time to test your dexterity with Honey Hands Challenge, a CBC game. Get ready for an adrenaline-fueled adventure as you navigate through tricky obstacles and master the art of precision as you collect all the honey without getting caught in sticky situations!
There’s a windmill there
It’s a Windmill puts your coordination to the test as you maneuver the ball through a maze of rotating windmill blades.
Putting the trap to work
The CBC game “Working the Trap” will challenge your problem-solving skills as you navigate through obstacles and strategically place traps to catch elusive creatures. Will you succeed in outsmarting them all?
We’re on the right track
Take control of your virtual car and navigate challenging tracks while avoiding obstacles and competing against other players. Speed, precision, and strategy are essential as you aim for victory in On Track to Win.
Group Study
You will need to use your problem-solving skills in “The Study Group”, a brain-teasing puzzle game. Embark on an exciting adventure with your friends as they solve complex riddles and uncover hidden clues. Are you ready to put your thinking cap on and crack the code? Let’s get started!
Rescue and search operations
The exciting CBC game “Search and Rescue” tests your problem-solving skills. Get ready for an adventure as you navigate through challenging puzzles, uncover hidden clues, and save the day! Can you find all the missing items and accomplish your mission on time?
It’s in the can
The CBC game “In the Can” challenges players to solve puzzles and navigate through an obstacle course. It features exciting gameplay and brain-teasing challenges, which will keep you entertained for hours.
Adventures in Detention
CBC’s Detention Adventure takes you on an exciting journey with Raign, Joy, Hulk, and Brett. Join them as they unravel mysteries, solve puzzles, and escape detention in this action-packed adventure! You’re about to embark on an epic quest as you unleash your inner detective skills!
Children of endlings
In “Endlings”, four foster children discover a hidden space ship and encounter mysterious creatures. Can they protect these endangered animals and prevent their extinction? Get ready for an epic adventure!
Murdoch, Macy
This exciting CBC game will challenge your detective skills. Join Macy Murdoch as she unravels mysteries, solves puzzles, and discovers hidden objects in her quest to become a top detective.
Sparks of a kind
Get ready to unlock your inner spark in “A Kind of Spark” a captivating CBC game that takes players on a journey of self-discovery. Join Mia as she navigates through challenges, discovers her unique abilities, and finds her place in the world.
Thrillists
A treasure trove of entertainment and excitement awaits you in the world of CBC Games. From mind-bending puzzles to thrilling adventures, there is something for everyone in this immersive gaming experience.
With an extensive selection of games across various genres, CBC Games has it all. Whether you’re a seasoned gamer or have just begun to explore the gaming world, you’ll never run out of options.
On CBC Games, you will find a unique and engaging experience with every game, from the heart-pounding action of Detention Adventure to the captivating mysteries of Macy Murdoch. As you progress, you will be able to unlock new levels and test your skills in each game.
In addition to gaming, CBC Games provides chances for education and development. Consider “A Kind of Spark,” an example that delves into crucial themes of inclusivity and acceptance, all within an enjoyable gaming encounter. It’s both entertaining and thought-provoking.
You will be scratching your head in wonder as you unravel each illusion in The Thrillusionists, a game that combines magic tricks with brain-teasers.
CBC Games brings you so many incredible games that unleashing your inner gamer has never been easier or more fun. So why wait? Dive into the world of gaming today and embark on unforgettable adventures from the comfort of your own home!
Whatever your gaming needs, CBC Games has you covered. So grab your controller (or keyboard) and get ready for hours upon hours of entertainment!
-
General10 months ago
Orchard Grass (Dactylis glomerata): A Botanical Epic
-
Lifestyle10 months ago
Fascinating World of ‘Cristoferideas’ and their Viral TikTok Video
-
Technology10 months ago
GPT66x: Boosting Talks with Transformer & Optimization
-
Gaming1 year ago
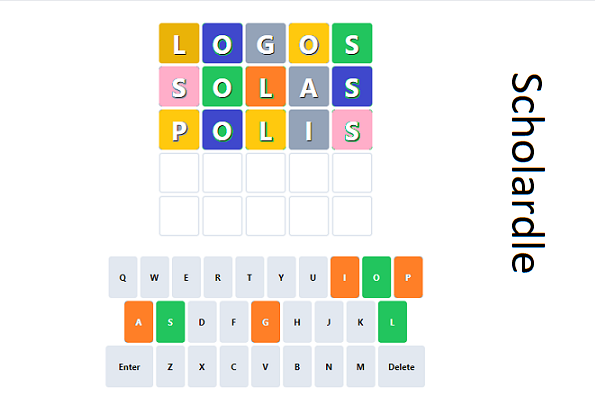
Scholardle: The Academic Word Guessing Game
-
Lifestyle10 months ago
Meet Katie Sakov San Francisco’s Talented Writer and Editor
-
Technology1 year ago
WHAT YOU SHOULD KNOW ABOUT PISIPHON VPN
-
Lifestyle10 months ago
Shine Bright with Mazalti: Jewelry Collections
-
Blog1 year ago
Record Of The Mightiest Lord Chapter 1